Technology is all about creating advancements in any subject. The fact that people can create these devices out of LEGO parts is even more amazing. This means that this popular building toy is being used as a real-world modeling tool.
Potentially everyone has the opportunity to become an inventor. The best part is that you don’t have to work out some of the more tedious aspects of designing. The base materials that are found in LEGO bricks have worked out things like precise measurements and the ability to make a consistent model.
It is one thing to make something that works. However, it is ten times more useful to be able to duplicate the gadget with ease. The following builders all are pushing the envelope of what’s possible.
Legotrope
The beginning of moving pictures started with things like the zoetrope. Chad Mealey wanted to see if this technology could be applied to a LEGO creation. The concept is that a number of frames are shown in quick succession. This tricks the human eye into thinking that you are seeing movement. Chad based his twelve frame motorized version on the Muybridge photos of a running horse.
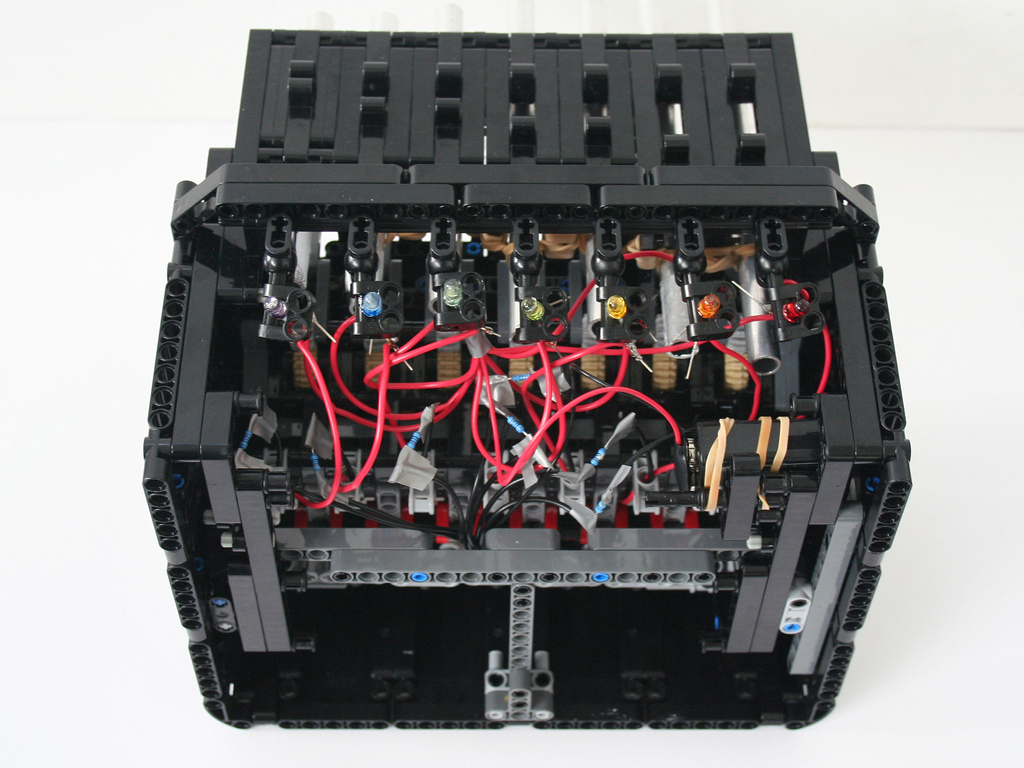
Ludwig Piano
Normally music is for those with the ability to hear. However, there is a concept known as induced synesthesia that attempts to engage other senses to enable the experience of music by the hearing impaired. Vimal Patel has developed a LEGO piano that displays lights along with the sound. This increased form of stimulus is meant to expand people’s enjoyment when played.
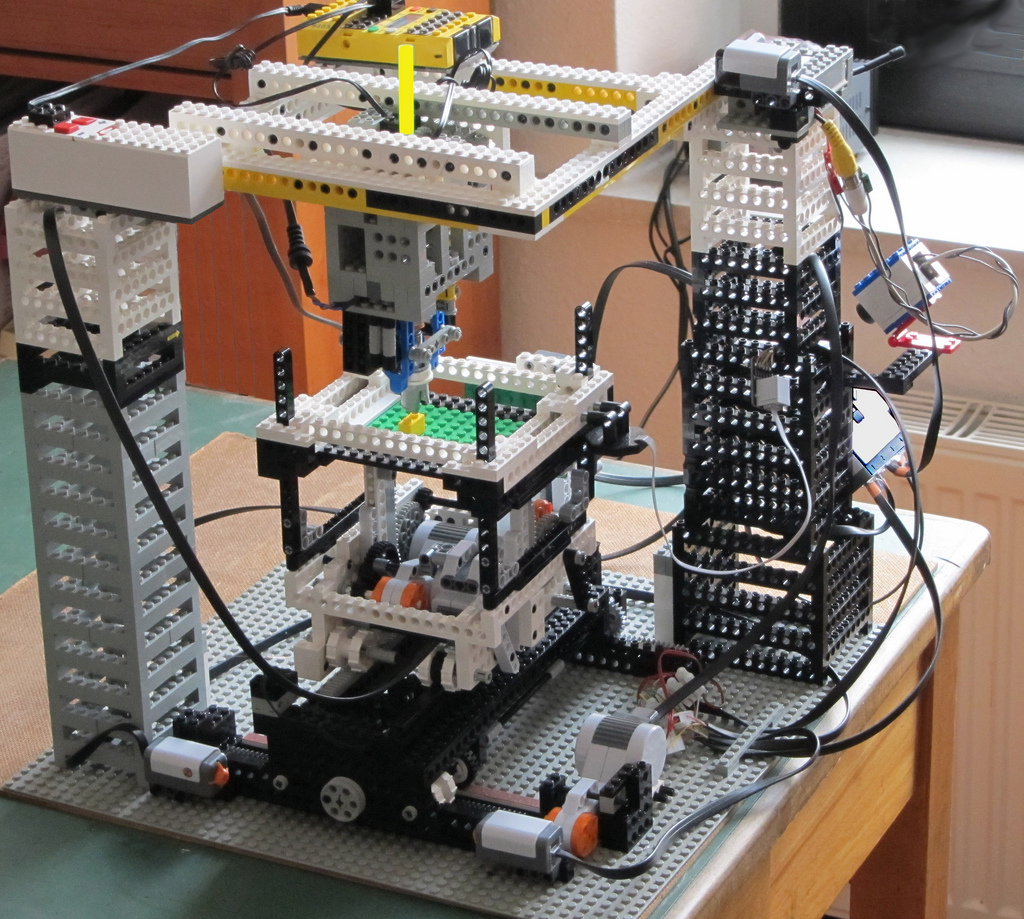
LEGO Mill NXT
Not many would think to make a device that could in turn make more pieces to build with. Jan Holthusen is not most people. His creation is a 3-D printer that can make objects. To do this, it requires a pliable material to work with. In this case, hot glue is melted and then ejected for the printing process. With this gadget, Jan has the capability to make some unique designs. Granted, they’d be made out of hot glue, but the end result is astounding.
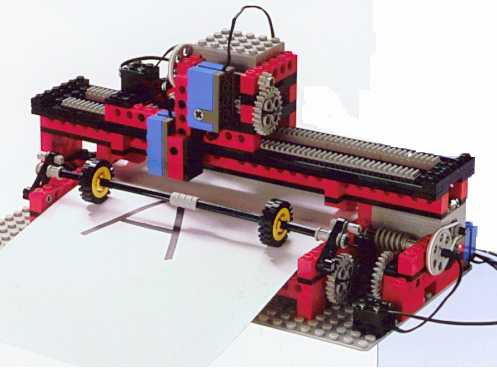
LEGO Printer
Not everyone has the need for a 3-D model. You are more likely to print something out on paper. Danilowille uses the various robotic options from LEGO Mindstorms to create a LEGO printer. Practically the only thing not made from LEGO bricks is the pen and paper it uses to write with.
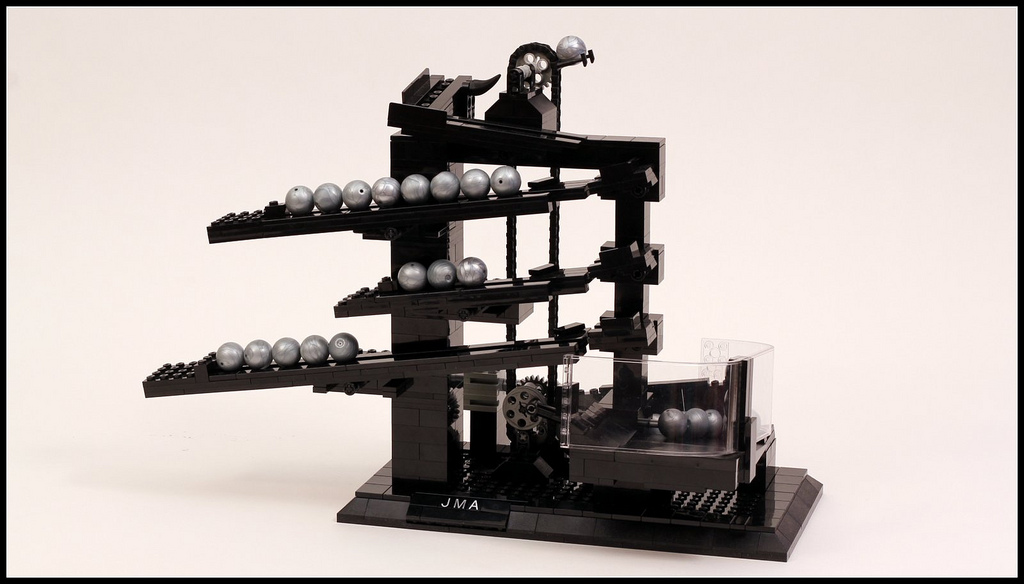
LEGO Ball Clock
Many people are familiar with the various ball contraptions fans have made with LEGO bricks. This is a slight variation of that process. JK Brickworks has created a specific type of clock he had as a child. The clock features three rows. Depending on where balls are on each row will tell you what time it is. The bottom row is hours, the middle row is ten minutes, and the top row is single minutes. As a row fills up, it deposits a ball into the row below before emptying into the reservoir, thus giving you the time in a quasi digital fashion.
Author
Carlo Pandian is an adult fan of LEGO and freelance writer, and his dream is to become a Master Model Builder at LEGOLAND Discovery Center Boston. When he’s not online, Carlo loves to learn new things such as Arduino and DIY design.